CrowdStrike Global Threat Report 2025: Key Findings on AI-Driven Cyber Attacks, Faster Breakout Times, and Rising Threat Landscape
Table of Contents
- CrowdStrike Global Threat Report 2025: Executive Overview and Key Statistics
- Breakout Time Reaches Record Lows: The 51-Second Threat
- Vishing Attacks Surge 442%: The New Social Engineering Frontier
- Generative AI in Cyberattacks: How Adversaries Weaponize Large Language Models
- China-Nexus Cyber Espionage: A 150% Surge in Activity
- Cloud Security Threats in the CrowdStrike Global Threat Report 2025
- Vulnerability Exploitation Trends: Exploit Chaining and Network Perimeter Attacks
- SaaS Exploitation and Access Broker Economy: The Emerging Threat Vectors
- Enterprise Defense Recommendations from the CrowdStrike Threat Report 2025
- What the CrowdStrike Global Threat Report 2025 Means for Your Organization
🔑 Key Takeaways
- CrowdStrike Global Threat Report 2025: Executive Overview and Key Statistics — The CrowdStrike 2025 Global Threat Report represents the industry’s most authoritative source on adversary intelligence, drawing from trillions of telemetry events processed by the AI-native CrowdStrike Falcon platform.
- Breakout Time Reaches Record Lows: The 51-Second Threat — One of the most alarming findings in the CrowdStrike global threat report 2025 is the continued acceleration of breakout times.
- Vishing Attacks Surge 442%: The New Social Engineering Frontier — Perhaps the most dramatic shift documented in the CrowdStrike 2025 Global Threat Report is the explosive growth of voice phishing, or vishing.
- Generative AI in Cyberattacks: How Adversaries Weaponize Large Language Models — Generative AI has emerged as a powerful force multiplier for cyber adversaries.
- China-Nexus Cyber Espionage: A 150% Surge in Activity —
CrowdStrike Global Threat Report 2025: Executive Overview and Key Statistics
The CrowdStrike 2025 Global Threat Report represents the industry’s most authoritative source on adversary intelligence, drawing from trillions of telemetry events processed by the AI-native CrowdStrike Falcon platform. The report examines the full spectrum of the cyber threat landscape — nation-state actors, eCrime groups, and hacktivists — and identifies the most significant trends shaping enterprise security.
Here are the headline statistics that every security professional needs to know:
- 48-minute average breakout time — down from 62 minutes in 2023, with the fastest recorded breakout at just 51 seconds
- 442% increase in vishing attacks between the first and second half of 2024
- 150% surge in China-nexus activity across all sectors, with targeted industries seeing 200-300% increases
- 79% of detections were malware-free, up from 40% in 2019, indicating a massive shift to hands-on-keyboard techniques
- 52% of vulnerabilities observed were related to initial access
- 50% year-over-year increase in access broker advertisements
- 35% of cloud incidents involved valid account abuse
- 26 new adversaries named in 2024, bringing the total tracked to 257
These numbers tell a clear story: the adversary ecosystem is professionalizing at an alarming rate. CrowdStrike’s Counter Adversary Operations team now tracks 257 named adversaries and more than 140 active malicious activity clusters — a scale of threat intelligence that underscores just how distributed and specialized modern cyber threats have become.
Breakout Time Reaches Record Lows: The 51-Second Threat
One of the most alarming findings in the CrowdStrike global threat report 2025 is the continued acceleration of breakout times. Breakout time — the interval between an adversary gaining initial access and beginning lateral movement across a network — is the critical window in which defenders must detect and respond to an intrusion.
In 2024, the average breakout time for interactive eCrime intrusions dropped to 48 minutes, down from 62 minutes the previous year. Even more concerning, the fastest breakout was recorded at just 51 seconds. That means defenders may have less than one minute to identify, assess, and neutralize an active threat before attackers establish deeper control over compromised systems.
The fastest breakout time CrowdStrike observed in 2024 was a mere 51 seconds — leaving defenders with virtually no margin for error.
This rapid escalation is driven by several factors. Adversaries are increasingly using legitimate remote monitoring and management (RMM) tools to access victim systems, making their activities blend seamlessly with normal IT operations. The shift away from traditional malware toward hands-on-keyboard techniques means that conventional signature-based detection often fails entirely. Organizations need real-time threat detection, robust identity and access controls, and proactive threat hunting to have any chance of catching these ultra-fast intrusions.
The case of CURLY SPIDER perfectly illustrates this speed. In one documented incident, the adversary completed their entire attack chain — from initial social engineering contact to establishing a persistent backdoor account — in under four minutes, without even needing to move laterally to another device. CrowdStrike OverWatch threat hunters detected and stopped the attack, but the incident demonstrates how narrow the window of opportunity has become for defenders.

Vishing Attacks Surge 442%: The New Social Engineering Frontier
Perhaps the most dramatic shift documented in the CrowdStrike 2025 Global Threat Report is the explosive growth of voice phishing, or vishing. Between the first and second halves of 2024, vishing detections increased by a staggering 442%, with a 40% compounded monthly growth rate throughout the year.
Vishing is devastatingly effective because it targets human psychology rather than software vulnerabilities. In a typical vishing campaign, threat actors call targeted users and impersonate IT support staff, claiming to resolve connectivity or security issues. Many campaigns begin with spam bombing — flooding the victim’s inbox with thousands of spam emails — which serves as the pretext for the follow-up call. The caller then guides the victim into installing a remote management tool like Microsoft Quick Assist or TeamViewer, granting the attacker direct access to the system.
The report identifies several sophisticated adversaries driving this trend:
- CURLY SPIDER — uses spam bombing followed by vishing calls, frequently collaborating with WANDERING SPIDER for Black Basta ransomware deployment
- CHATTY SPIDER — employs callback phishing for data theft and extortion, primarily targeting legal and insurance sectors with demands up to $8 million
- PLUMP SPIDER — targets Brazilian organizations through vishing to conduct wire fraud using compromised payment systems
- SCATTERED SPIDER — pioneers help desk social engineering, calling IT help desks while impersonating legitimate employees to reset passwords and MFA
Help desk social engineering represents a particularly concerning evolution. Threat actors call an organization’s IT help desk impersonating a legitimate employee, accurately answering security questions using information gathered from public resources, social media, and underground markets. Calls are typically made outside business hours to maximize the time before the legitimate account owner notices suspicious activity. The Cybersecurity and Infrastructure Security Agency (CISA) has repeatedly warned about the growing sophistication of social engineering threats facing organizations.
📊 Explore this analysis with interactive data visualizations
Generative AI in Cyberattacks: How Adversaries Weaponize Large Language Models
Generative AI has emerged as a powerful force multiplier for cyber adversaries. The CrowdStrike global threat report 2025 documents how nation-state, eCrime, and hacktivist actors across all major categories have become early and avid adopters of off-the-shelf chatbots and LLMs to enhance their operations.
The applications of genAI in cyberattacks are both broad and deeply concerning:
Social Engineering at Scale
DPRK-nexus adversary FAMOUS CHOLLIMA uses genAI to create fictitious LinkedIn profiles with AI-generated text and fake profile images, supporting their malicious insider campaigns. LLMs help generate plausible interview responses when their operatives apply for software development positions at target companies. In 2024, CrowdStrike OverWatch responded to 304 FAMOUS CHOLLIMA incidents, with nearly 40% representing insider threat operations.
Deepfake technology powered by generative AI enabled a particularly striking business email compromise (BEC) attack in 2024. Threat actors used public footage to create credible deepfake video clones of a company’s CFO, successfully social engineering a victim into transferring $25.6 million.
Phishing Effectiveness Multiplied
Academic research cited in the report reveals that LLM-generated phishing messages achieved a 54% click-through rate, compared to just 12% for human-written phishing messages. This five-fold increase in effectiveness demonstrates how generative AI is fundamentally changing the threat equation for email-based attacks. The research published on arXiv validates the growing concern around AI-enhanced social engineering.
Malware Development and Disinformation
Adversaries are also using LLMs to generate malware scripts, create decoy websites, and conduct large-scale information operations. China-aligned LLM-powered networks like Green Cicada coordinated inauthentic behavior across social media platforms, while Russia-aligned operators used genAI to spread disinformation targeting U.S. audiences during the 2024 election cycle.
Cloud-conscious threat actors have begun exploring a new frontier: LLMJacking. In this attack pattern, adversaries exploit stolen cloud credentials to access AI services, then resell that access to other threat actors for malicious purposes. This emerging criminal market around unauthorized LLM access represents a novel convergence of cloud security and AI security risks.
China-Nexus Cyber Espionage: A 150% Surge in Activity
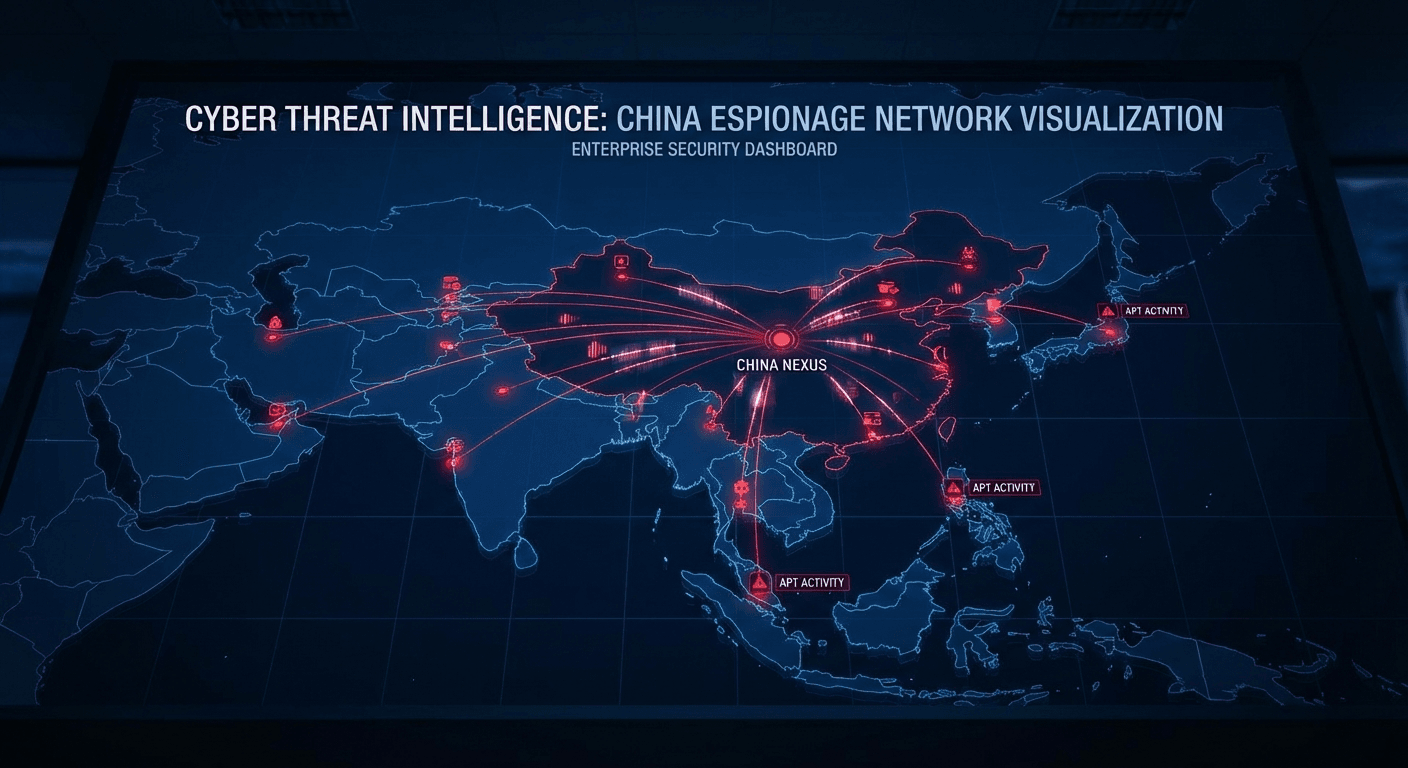
China’s cyber espionage capabilities reached an inflection point in 2024. The CrowdStrike 2025 Global Threat Report documents a 150% increase in China-nexus activity across all sectors, with the most targeted industries — financial services, media, manufacturing, and industrials and engineering — experiencing 200-300% increases compared to previous years.
This dramatic escalation reflects decades of strategic investment by the Chinese government into its cyber workforce and programs. General Secretary Xi Jinping’s 2014 call for China to become a “cyber power” (网络强国) and the CCP’s grand strategy of national rejuvenation (伟大复兴) have yielded matured capabilities that are now being deployed at unprecedented scale.
The ecosystem supporting China’s cyber operations includes:
- University programs producing a highly trained cyber workforce
- Private sector contracting pipelines supporting PLA, MPS, and MSS cyber units
- Vulnerability discovery competitions and bug hunts that feed CCP-controlled exploit programs
- Industry networking enabling shared tooling and tradecraft across adversary groups
- Operational relay box (ORB) networks consisting of hundreds or thousands of compromised devices for anonymization
CrowdStrike graduated seven new China-nexus adversaries in 2024, five of which demonstrate unique specialization: LIMINAL PANDA, LOCKSMITH PANDA, and OPERATOR PANDA focus on telecommunications; VAULT PANDA targets financial services globally; and ENVOY PANDA targets diplomatic entities in Africa and the Middle East. This shift from “smash-and-grab” operations to increasingly focused and mission-specific intrusions marks a new era in Chinese cyber operations. The Office of the Director of National Intelligence has similarly highlighted China as a top-tier cyber threat to U.S. interests.
Cloud Security Threats in the CrowdStrike Global Threat Report 2025
The cloud threat landscape is expanding rapidly. New and unattributed cloud intrusions increased 26% compared to 2023, as more threat actors — both nation-state and eCrime — seek to exploit cloud services for data theft, ransomware deployment, and persistent access.
A critical finding is that valid account abuse now accounts for 35% of cloud incidents, making it the primary initial access vector to cloud environments. Attackers are increasingly using stealth-oriented tactics to access credentials without changing them, which would alert the legitimate user. Information stealers like Stealc and Vidar were updated in 2024 to specifically target cloud accounts, providing attackers with instant access to cloud credentials.
Key cloud security trends from the report include:
- SCATTERED SPIDER’s share of cloud intrusions dropped from 30% to 13%, not because they slowed down, but because numerous other actors entered the cloud threat space
- China-nexus cloud intrusions increased 6% across multiple services including Alibaba and Azure
- DPRK-nexus actors like LABYRINTH CHOLLIMA compromised developer workstations via backdoored GitHub projects before pivoting to cloud using cached credentials
- Password spraying evolved significantly, with China-nexus ORB07 exploiting authentication flow bugs to validate credentials without logging successful sign-in events
- Defense evasion tactics intensified, with indicator removal being the most common method — used in approximately 75-78% of evasion cases
Organizations can learn more about protecting their cloud environments by reviewing the NIST Cloud Security Guidelines (SP 800-210), which provide a comprehensive framework for securing cloud infrastructure and data.
📊 Explore this analysis with interactive data visualizations
Vulnerability Exploitation Trends: Exploit Chaining and Network Perimeter Attacks
The vulnerability landscape in the CrowdStrike global threat report 2025 reveals that 52% of observed vulnerabilities were related to initial access — reinforcing the critical importance of securing exposed systems before attackers gain a foothold. Adversaries continued to target devices at the network periphery, where traditional endpoint detection and response (EDR) visibility is limited.
Two particularly dangerous trends emerged in 2024:
Exploit Chaining
Threat actors increasingly combined two or more exploits to create seamless attack sequences achieving unauthenticated remote code execution (RCE). Notable examples include chaining a bypass vulnerability with a privilege escalation flaw in Palo Alto Networks PAN-OS, and OPERATOR PANDA chaining two Cisco IOS vulnerabilities to target U.S. telecom entities. This approach undermines severity-score-based patching because the individual vulnerabilities may receive less attention than they deserve when considered in combination.
Abusing Legitimate Features
Adversaries combined vulnerability exploitation with abuse of built-in product features to achieve RCE. Microsoft SQL Server’s xp_cmdshell — disabled by default due to known security concerns — was exploited across multiple products, indicating threat actors are increasingly employing living-off-the-land techniques.
The report also highlights the discovery-rediscovery-circumvention trend: once a vulnerability is disclosed in a particular component, threat actors explore the same attack surface for additional flaws. The mskssrv driver example is striking — a single Pwn2Own exploitation in March 2023 led to at least 16 subsequent vulnerability disclosures as researchers and threat actors piled onto the newly revealed attack surface.
SaaS Exploitation and Access Broker Economy: The Emerging Threat Vectors
The CrowdStrike 2025 Global Threat Report identifies SaaS exploitation as a critical threat to watch. Throughout 2024, multiple adversaries leveraged access to cloud-based SaaS applications — including Microsoft 365, SharePoint, and SSO-integrated platforms — to steal data, facilitate lateral movement, and enable downstream attacks on third parties.
The access broker economy has become a thriving underground marketplace. Access broker advertisements increased 50% year-over-year, with 4,486 total advertisements tracked in 2024. These specialists acquire access to organizations and sell it to other threat actors, including ransomware operators. The professionalization of this supply chain means that even less sophisticated attackers can purchase high-quality initial access to well-defended organizations.
SCATTERED SPIDER demonstrated the cascading impact of SaaS compromise: after gaining SSO access, the adversary tested access to all available integrated applications, searching for credentials, network architecture documentation, cyber insurance details, and revenue information. In one case, they obtained API keys to a commercial SMS distribution application and used it to send more than 700,000 SMS messages containing phishing and cryptocurrency drainer links.
The customer database compromise campaign of mid-2024 showed that SaaS exploitation doesn’t always require a broader network breach. Threat actors used compromised credentials from information stealer logs — widely available in eCrime channels — to directly access cloud database instances that lacked MFA protections. For more insights on how interactive content can help organizations communicate complex security concepts, explore our interactive library of enterprise reports.
Enterprise Defense Recommendations from the CrowdStrike Threat Report 2025
The CrowdStrike 2025 Global Threat Report concludes with five strategic recommendations that every organization should prioritize:
- Secure the entire identity ecosystem — Adopt phishing-resistant MFA solutions such as hardware security keys. Implement just-in-time access, regular account reviews, and conditional access controls. Deploy identity threat detection tools that monitor behavior across endpoints, cloud, and SaaS environments.
- Eliminate cross-domain visibility gaps — Deploy XDR and next-generation SIEM solutions that provide unified visibility across endpoints, networks, cloud environments, and identity systems. Integrate proactive threat hunting and real-time threat intelligence.
- Defend the cloud as core infrastructure — Implement cloud-native application protection platforms (CNAPPs) with cloud detection and response (CDR) capabilities. Enforce strict role-based access and conditional policies. Conduct regular audits to uncover overly permissive settings and unpatched vulnerabilities.
- Prioritize vulnerabilities with an adversary-centric approach — Focus patching on frequently targeted internet-facing services. Monitor for signs of exploit chaining. Use AI-driven prioritization to reduce noise and focus on the vulnerabilities that affect critical systems.
- Know your adversary and be prepared — Adopt intelligence-driven defense by understanding which adversaries target your industry, how they operate, and what their objectives are. Build incident response plans that account for sub-minute breakout times.
These recommendations align closely with the frameworks published by the National Institute of Standards and Technology (NIST) Cybersecurity Framework, which provides industry-recognized guidelines for improving critical infrastructure cybersecurity. Organizations looking to operationalize these findings can also explore how Libertify transforms complex reports into interactive experiences that make threat intelligence accessible to all stakeholders.
What the CrowdStrike Global Threat Report 2025 Means for Your Organization
The overarching message of the CrowdStrike 2025 Global Threat Report is clear: the adversary is advancing faster than most organizations are adapting. The shift toward identity-based attacks, the weaponization of generative AI, the professionalization of the access broker economy, and the unprecedented speed of breakout times all point to a threat landscape that demands fundamental changes in how enterprises approach cybersecurity.
For security leaders, several immediate actions should be prioritized:
- Reassess your mean time to detect and respond — with 51-second breakouts now documented, manual playbooks are insufficient. Automated detection and response capabilities are no longer optional.
- Train your workforce against vishing — the 442% increase in vishing means that employee awareness training must now include telephone-based social engineering scenarios, not just email phishing.
- Audit your cloud identity posture — with 35% of cloud incidents involving valid account abuse, the security of cloud credentials is arguably the single most important defensive priority.
- Implement defense-in-depth for network perimeter devices — the continued targeting of VPNs, firewalls, and network appliances requires layered controls beyond simple patching.
- Monitor the access broker marketplace — understanding whether your organization’s access is being advertised on underground forums provides critical early warning of impending attacks.
The CrowdStrike 2025 Global Threat Report is not just another industry publication — it is a roadmap of where adversaries are heading and a blueprint for how defenders must respond. Organizations that act on these findings will be better positioned to defend against the enterprising adversaries of 2025. Those that don’t may find themselves among the statistics in next year’s report.
For more in-depth analyses of cybersecurity and enterprise technology trends, visit our Interactive Library where we transform leading industry reports into engaging, interactive experiences.
📊 Explore this analysis with interactive data visualizations
Frequently Asked Questions
What are the key findings of the CrowdStrike 2025 Global Threat Report?
The CrowdStrike 2025 Global Threat Report reveals that average breakout time dropped to 48 minutes (fastest at 51 seconds), vishing attacks surged 442%, China-nexus cyber activity increased 150%, 79% of detections were malware-free, and generative AI is increasingly used in cyberattack campaigns.
How fast can cyber attackers move laterally in a network in 2025?
According to CrowdStrike’s 2025 threat report, the average eCrime breakout time fell to 48 minutes, with the fastest observed breakout taking just 51 seconds. This means defenders may have less than a minute to detect and respond before attackers establish deeper control over compromised systems.
Why are vishing attacks increasing in cybersecurity?
Vishing attacks grew 442% between the first and second half of 2024 because they exploit human psychology rather than technical vulnerabilities. Adversaries impersonate IT support staff and use techniques like spam bombing to create urgency, making victims more likely to grant remote access or share credentials.
How is generative AI being used in cyberattacks?
Adversaries use generative AI to create convincing phishing emails with 54% click-through rates (vs. 12% for human-written), generate deepfake videos for business email compromise, produce fake IT job candidate profiles, write malware scripts, create decoy websites, and conduct large-scale disinformation campaigns.
What industries are most targeted by cyber threats in 2025?
According to the CrowdStrike 2025 Global Threat Report, the technology sector remains the most targeted industry for the seventh consecutive year, followed by consulting and professional services, manufacturing, retail, and financial services. China-nexus attacks on financial services, media, manufacturing, and engineering sectors increased 200-300%.





