—
0:00
ESMA Cloud Outsourcing Guidelines 2025: Complete Regulatory Compliance Guide
Table of Contents
- Understanding the ESMA Cloud Outsourcing Guidelines 2025 Revision
- DORA and Cloud Outsourcing: The Regulatory Convergence
- Who Must Comply: Revised Scope of the ESMA Cloud Guidelines
- The 9 ESMA Cloud Outsourcing Guidelines Explained
- Information Security and Data Protection in Cloud Outsourcing
- Exit Strategies and Business Continuity Requirements
- Audit Rights and Sub-Outsourcing Controls
- Regulatory Notification and Supervisory Framework
- Cloud Outsourcing Risk Assessment: Critical vs. Non-Critical Functions
- Implementation Roadmap for Compliance Teams
🔑 Key Takeaways
- Understanding the ESMA Cloud Outsourcing Guidelines 2025 Revision — On 11 July 2025, the European Securities and Markets Authority (ESMA) published its Final Report on revised Guidelines on outsourcing to cloud service providers (ESMA65-294529287-2639).
- DORA and Cloud Outsourcing: The Regulatory Convergence — The relationship between DORA and the ESMA cloud outsourcing guidelines represents a textbook case of regulatory consolidation in European financial services.
- Who Must Comply: Revised Scope of the ESMA Cloud Guidelines — The most significant change in the revised ESMA cloud outsourcing guidelines is the narrowing of their addressee scope.
- The 9 ESMA Cloud Outsourcing Guidelines Explained — While the scope has narrowed, the substantive content of the ESMA cloud outsourcing guidelines remains unchanged from the 2021 version.
- Information Security and Data Protection in Cloud Outsourcing — Guideline 4: Information Security addresses the technical and organizational measures that firms must implement to protect data and systems in cloud environments.
Understanding the ESMA Cloud Outsourcing Guidelines 2025 Revision
On 11 July 2025, the European Securities and Markets Authority (ESMA) published its Final Report on revised Guidelines on outsourcing to cloud service providers (ESMA65-294529287-2639). This critical regulatory update represents the most significant evolution of the EU’s cloud outsourcing framework since the original guidelines were published in 2020 and became applicable in 2021. For financial services firms operating in the European Union, understanding these revised guidelines is essential for maintaining regulatory compliance and managing operational risk.
The revision was driven by a singular regulatory development: the application of the Digital Operational Resilience Act (DORA), Regulation (EU) 2022/2554, which became applicable on 17 January 2025. DORA represents a comprehensive consolidation of the EU’s legal framework on digital operational resilience, covering ICT third-party risk management across the entire financial services sector. Because DORA now addresses the subject matter previously covered by the 2021 ESMA cloud outsourcing guidelines, the revised framework narrows its scope while maintaining critical protections for entities outside DORA’s reach.
The practical impact of this revision is both clarifying and simplifying. For the majority of financial entities—investment firms, credit institutions, insurance companies, and fund managers—the ESMA cloud outsourcing guidelines have been superseded by DORA’s more comprehensive requirements. However, for certain depositaries under the Alternative Investment Fund Managers Directive (AIFMD) and the Undertakings for Collective Investment in Transferable Securities Directive (UCITSD) that fall outside DORA’s scope, the revised guidelines maintain essential cloud outsourcing governance standards.
DORA and Cloud Outsourcing: The Regulatory Convergence
The relationship between DORA and the ESMA cloud outsourcing guidelines represents a textbook case of regulatory consolidation in European financial services. Prior to DORA, cloud outsourcing governance was fragmented across multiple sector-specific guidelines and directives, creating compliance complexity for firms operating across multiple regulatory regimes. DORA’s arrival on 17 January 2025 unified this landscape under a single, harmonized framework for digital operational resilience.
DORA covers “a wide range of ICT third-party service providers, including providers of cloud computing services, software, data analytics services and providers of data centre services,” as stated in its recital 63. The regulation aims to address what it identifies as “a certain lack of homogeneity and convergence regarding the monitoring of ICT third-party risk and ICT third-party dependencies.” This comprehensive scope means that most financial entities previously subject to the ESMA cloud outsourcing guidelines now operate under DORA’s more detailed and legally binding requirements.
For compliance teams navigating this transition, the key insight is that DORA doesn’t merely replace the ESMA guidelines—it significantly expands the regulatory expectations for ICT risk management. DORA introduces mandatory incident reporting, standardized contractual requirements for critical ICT third-party providers, and a new oversight framework for systemically important service providers. Our analysis of the Financial Services Regulatory Outlook 2026 provides additional context on how DORA is reshaping the broader compliance landscape for European financial institutions.

Who Must Comply: Revised Scope of the ESMA Cloud Guidelines
The most significant change in the revised ESMA cloud outsourcing guidelines is the narrowing of their addressee scope. The guidelines now apply exclusively to two categories of depositaries that fall outside DORA’s reach:
First, depositaries of alternative investment funds (AIFs) referred to in Article 21(3)(c) and Article 21(3), third subparagraph, of the AIFMD, where they are not financial entities to which DORA applies. Second, depositaries of UCITS referred to in Article 23(2)(c) of the UCITS Directive, where they are not financial entities to which DORA applies.
This targeted scope reflects ESMA’s proportionality analysis. These depositaries serve a critical function within the asset management sector, overseeing the safekeeping of fund assets and the supervision of fund operations. Despite their exclusion from DORA, their market relevance, particularly in certain EU jurisdictions, and the characteristics of the funds they serve—including the size of assets under management and the presence of retail investors—justify maintaining dedicated cloud outsourcing guidelines.
The practical implication is clear: if your organization is a financial entity within the scope of Article 2 of DORA, the ESMA cloud outsourcing guidelines no longer apply to you. Your cloud outsourcing obligations are now governed exclusively by DORA and its implementing technical standards. However, if you are a depositary falling within the categories described above, compliance with the revised ESMA guidelines remains mandatory.
📊 Explore this analysis with interactive data visualizations
The 9 ESMA Cloud Outsourcing Guidelines Explained
While the scope has narrowed, the substantive content of the ESMA cloud outsourcing guidelines remains unchanged from the 2021 version. The nine guidelines establish a comprehensive framework for managing cloud outsourcing risk that continues to represent best practice even for entities now covered by DORA. Understanding these guidelines provides essential context for interpreting DORA’s more detailed requirements.
Guideline 1: Governance, Oversight and Documentation requires firms to establish clear governance arrangements for cloud outsourcing decisions, including defined roles and responsibilities, documented policies, and regular management body oversight. Cloud outsourcing arrangements must be integrated into the firm’s overall risk management framework, with clear escalation procedures and reporting lines. This governance foundation ensures that cloud outsourcing decisions are made with appropriate institutional awareness and accountability.
Guideline 2: Pre-Outsourcing Analysis and Due Diligence mandates a thorough assessment before entering any cloud outsourcing arrangement. Firms must evaluate the risks associated with the planned outsourcing, including concentration risk, country risk, and the cloud service provider’s (CSP) ability to meet the firm’s requirements. The due diligence process must consider whether the function being outsourced is critical or important, as this classification triggers enhanced requirements throughout the guidelines.
Guideline 3: Key Contractual Elements specifies the minimum provisions that must be included in cloud outsourcing agreements. These include clear service level descriptions, data protection and processing obligations, audit rights, business continuity and exit plan provisions, and termination rights. The contractual framework serves as the primary mechanism for firms to maintain control over outsourced functions and ensure that CSP obligations are legally enforceable.
Information Security and Data Protection in Cloud Outsourcing
Guideline 4: Information Security addresses the technical and organizational measures that firms must implement to protect data and systems in cloud environments. This includes encryption requirements for data at rest and in transit, access management controls, network security measures, and incident detection and response capabilities. Firms must ensure that the CSP’s security measures meet the firm’s own security standards and that security controls are subject to regular testing and validation.
The information security guideline is particularly relevant in the context of increasing cyber threats targeting the financial sector. Cloud environments present unique security challenges, including shared infrastructure risks, API vulnerabilities, and the complexity of multi-tenant architectures. Firms must develop security monitoring capabilities that provide visibility into cloud-hosted operations and enable rapid detection and response to security incidents.
Data protection considerations extend beyond pure security to encompass GDPR compliance, data residency requirements, and cross-border data transfer restrictions. The intersection of cloud outsourcing with data protection regulation creates compliance complexity that requires coordinated oversight across IT security, legal, and compliance functions. For organizations assessing these risks in the broader context of financial sector resilience, our analysis of banking risk management trends in 2025 provides complementary perspective on how financial institutions are strengthening their operational resilience frameworks.
Exit Strategies and Business Continuity Requirements
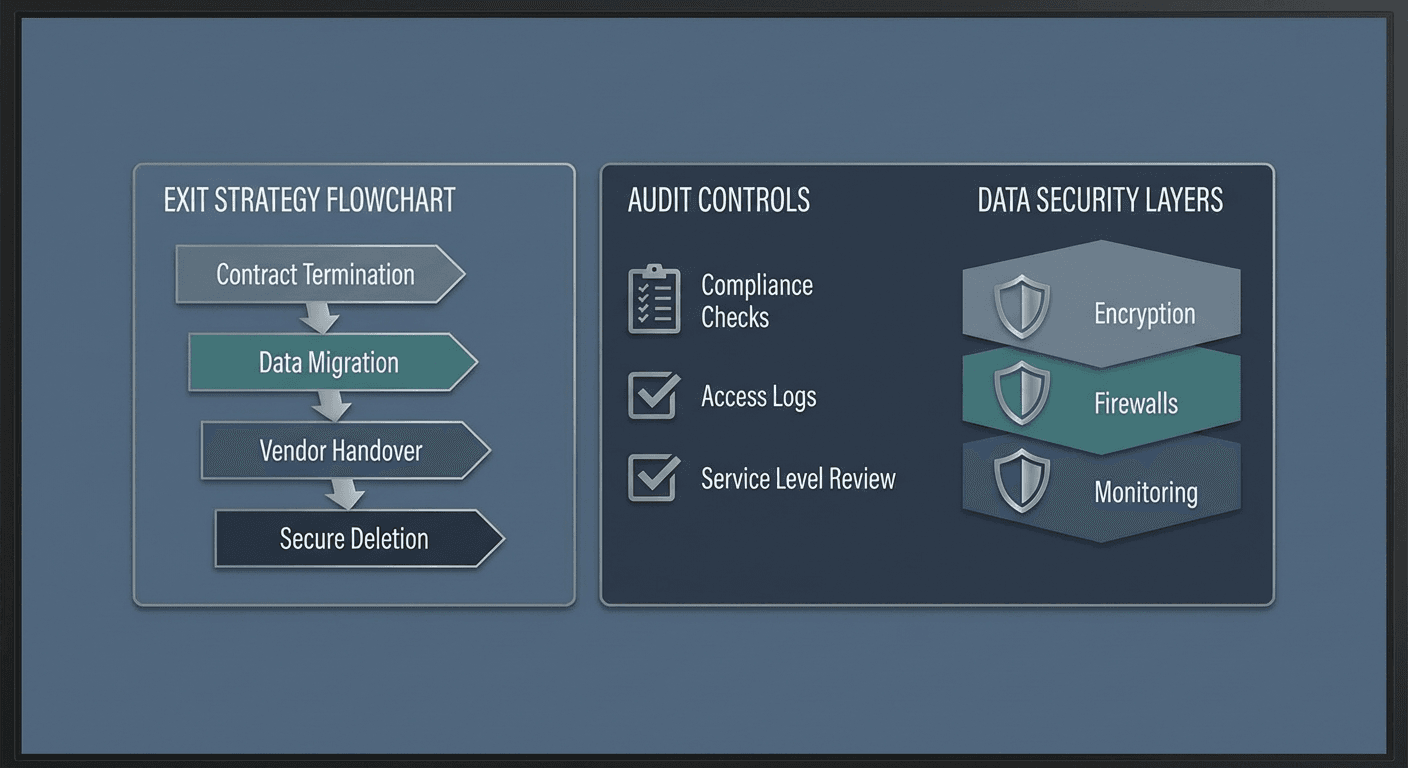
Guideline 5: Exit Strategies requires firms to develop and maintain comprehensive exit plans before entering cloud outsourcing arrangements. These exit strategies must address how the firm will transition services away from a CSP in both planned and unplanned scenarios, including provider failure, contract termination, and significant service degradation. The exit plan must include data migration procedures, timeline estimates, and resource requirements, and must be regularly tested and updated.
Exit strategy requirements reflect ESMA’s recognition that cloud vendor lock-in represents a significant operational risk for financial services firms. The high degree of standardization in cloud services, while beneficial for cost efficiency, can create dependencies that are difficult to unwind. Firms must ensure that their cloud architectures support portability, that data can be extracted in usable formats, and that alternative service arrangements can be activated within timeframes that maintain business continuity.
The exit strategy guideline connects directly to the broader concentration risk concerns that have driven much of the EU’s regulatory attention to cloud outsourcing. When multiple financial entities rely on the same small number of CSPs, the failure of a single provider could have systemic implications. Exit strategies serve as a critical mitigation against this concentration risk, ensuring that individual firms can maintain operations even in severe disruption scenarios.
📊 Explore this analysis with interactive data visualizations
Audit Rights and Sub-Outsourcing Controls
Guideline 6: Access and Audit Rights establishes that firms must retain effective access to data processed by CSPs and must secure contractual audit rights that enable both the firm and its competent authority to audit the CSP’s operations. These rights must be proportionate to the criticality of the outsourced function but must ensure that the firm maintains sufficient oversight to verify compliance with contractual and regulatory obligations.
Audit rights in cloud environments present practical challenges that the guidelines acknowledge. The scale and standardization of cloud services mean that individual client audits may be impractical or disruptive. The guidelines therefore permit the use of pooled audits, third-party certifications (such as ISO 27001 or SOC 2), and CSP-provided audit reports as alternative mechanisms for satisfying audit requirements. However, firms must retain the contractual right to conduct their own audits when necessary, particularly for critical or important functions.
Guideline 7: Sub-Outsourcing addresses the risk that CSPs may delegate parts of their services to sub-contractors, potentially creating opaque supply chains that undermine the firm’s oversight capabilities. Firms must ensure that their agreements with CSPs include provisions governing sub-outsourcing, including notification requirements, approval rights for material sub-outsourcing, and flow-down of key contractual obligations to sub-contractors. This guideline is essential for maintaining visibility across the entire cloud service delivery chain.
Regulatory Notification and Supervisory Framework
Guideline 8: Written Notification to Competent Authorities requires firms to notify their supervisory authority of cloud outsourcing arrangements involving critical or important functions. The notification must include sufficient information for the authority to assess the risk profile of the arrangement, including the identity of the CSP, the nature of the outsourced function, and the jurisdictions involved. This notification requirement enables competent authorities to maintain oversight of cloud outsourcing trends and concentration risks across the entities they supervise.
Guideline 9: Supervision of Cloud Outsourcing Arrangements is addressed to competent authorities rather than firms, providing guidance on how supervisory bodies should oversee and assess cloud outsourcing arrangements. This includes expectations for supervisory review processes, risk-based prioritization of supervisory activities, and coordination among authorities when cloud outsourcing arrangements span multiple jurisdictions.
The supervisory framework established by Guideline 9 is particularly relevant in the context of DORA’s new oversight regime for critical ICT third-party service providers. While the revised ESMA guidelines apply to a narrower set of entities, the supervisory principles they establish remain influential in shaping how national competent authorities approach cloud outsourcing oversight across their regulatory remit. For organizations tracking the evolution of EU financial regulation, our coverage of the MiCA regulation framework illustrates how these supervisory principles extend to emerging digital asset markets.
Cloud Outsourcing Risk Assessment: Critical vs. Non-Critical Functions
A foundational concept running through the ESMA cloud outsourcing guidelines is the distinction between critical or important functions and non-critical functions. This classification determines the intensity of requirements that apply to a particular outsourcing arrangement and serves as the primary mechanism for applying the principle of proportionality throughout the framework.
Functions are classified as critical or important based on their significance to the firm’s ability to operate, meet regulatory obligations, and protect clients. Factors to consider include the function’s impact on revenue generation, the firm’s ability to continue operations if the function were disrupted, and whether the function involves the processing of confidential or personal data. For depositaries specifically, functions related to asset safekeeping, ownership verification, and oversight of fund operations are likely to be classified as critical or important.
When a function is classified as critical or important, the guidelines impose enhanced requirements across virtually every dimension—from the depth of pre-outsourcing due diligence to the specificity of contractual provisions, the rigor of security measures, and the comprehensiveness of exit strategies. This tiered approach ensures that regulatory requirements are proportionate to risk, avoiding excessive compliance burden for low-risk outsourcing arrangements while maintaining rigorous oversight of arrangements that could impact financial stability or investor protection.
Implementation Roadmap for Compliance Teams
For depositaries within the revised scope, the implementation path is straightforward—these entities were already subject to the 2021 guidelines and need not implement new controls. The key action is to ensure that existing cloud outsourcing governance arrangements remain current and aligned with the unchanged substantive requirements. Compliance teams should document their assessment confirming that the entity falls within the revised scope and update internal policies to reference the 2025 amended guidelines rather than the 2021 version.
For entities transitioning to DORA compliance, the ESMA cloud outsourcing guidelines provide a valuable benchmarking tool. While DORA’s requirements are more comprehensive, the nine-guideline structure of the ESMA framework offers a clear checklist for verifying that cloud outsourcing arrangements meet the minimum standards expected by EU regulators. Organizations that achieved full compliance with the ESMA guidelines will find that they have a strong foundation for DORA compliance, though gap analysis against DORA’s more detailed requirements is essential.
The broader market trend is toward greater standardization and automation of cloud outsourcing compliance processes. Financial services firms are investing in governance, risk, and compliance (GRC) platforms that can map cloud outsourcing arrangements against multiple regulatory frameworks simultaneously—addressing ESMA guidelines, DORA requirements, GDPR obligations, and national regulatory expectations within a unified compliance management system. This integrated approach reduces compliance costs while improving oversight quality, a priority highlighted in the BCG Global Asset Management Report 2024 as essential for maintaining competitive margins in the face of increasing regulatory complexity.
📊 Explore this analysis with interactive data visualizations
Frequently Asked Questions
What are the ESMA cloud outsourcing guidelines 2025?
The ESMA cloud outsourcing guidelines 2025 are revised regulatory standards published on 11 July 2025 that update the 2021 guidelines on outsourcing to cloud service providers. The revision narrows the scope to depositaries under AIFMD and UCITSD that are not covered by DORA, while maintaining the same substantive compliance requirements for governance, risk management, and security.
How does DORA affect the ESMA cloud outsourcing guidelines?
The Digital Operational Resilience Act (DORA), applicable since January 2025, supersedes the ESMA cloud outsourcing guidelines for most financial entities. DORA provides a comprehensive framework for ICT risk management that covers cloud outsourcing. The revised ESMA guidelines now only apply to certain depositaries under AIFMD and UCITSD that fall outside DORA’s scope.
What are the 9 guidelines for cloud outsourcing under ESMA?
The 9 ESMA guidelines cover: 1) Governance, oversight and documentation, 2) Pre-outsourcing analysis and due diligence, 3) Key contractual elements, 4) Information security, 5) Exit strategies, 6) Access and audit rights, 7) Sub-outsourcing, 8) Written notification to competent authorities, and 9) Supervision of cloud outsourcing arrangements.
Which entities must comply with the revised ESMA cloud guidelines?
The revised guidelines apply specifically to depositaries of alternative investment funds (AIFs) under Article 21(3)(c) of AIFMD and depositaries of UCITS under Article 23(2)(c) of the UCITS Directive, but only where these entities are not financial entities to which DORA applies. Most other financial entities are now covered by DORA instead.
What exit strategy requirements does ESMA mandate for cloud outsourcing?
ESMA requires firms to develop comprehensive exit strategies before entering cloud outsourcing arrangements. These must include transition plans, data migration procedures, continuity measures, and timelines that ensure critical functions can be maintained during provider transitions. Exit strategies must be documented, regularly tested, and updated to reflect changes in the firm’s operations.




